Understanding how different vendors classify and track threat actor groups is essential for analysts, red teamers, and defenders working with threat intelligence. However, it can get confusing the same group might have multiple names depending on who’s doing the tracking. This inconsistency often stems from the fact that threat actors reuse infrastructure, borrow TTPs, or intentionally try to mislead attribution efforts.
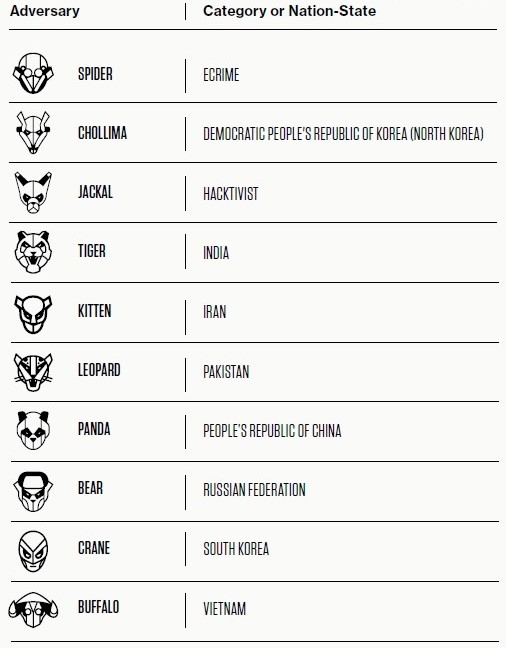
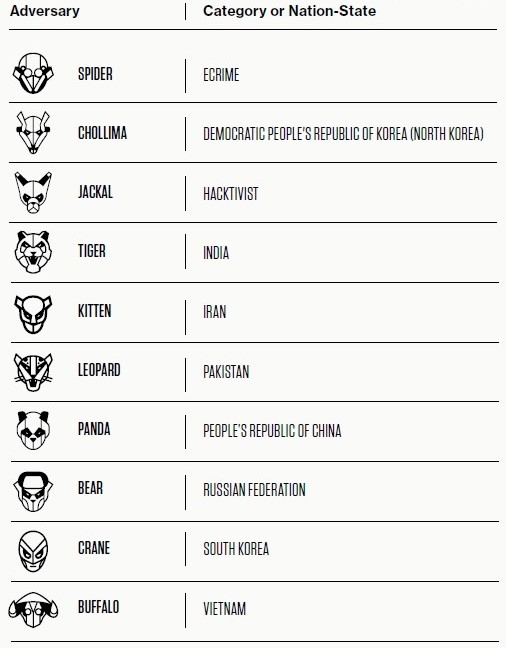
CrowdStrike classifies adversaries using animal-themed names, based on either their geopolitical origin (for nation-states) or intent/motivation (for non-nation-state actors).
Mandiant (now part of Google Cloud) uses a more structured and numerical naming convention, relying on prefixes that reflect actor type or investigation status.
| Prefix | Country | Examples |
|---|---|---|
| APT1, 2, 3... | China | APT1, APT3, APT10, APT41 |
| APT28, 29 | Russia | APT28 (Fancy Bear) |
| APT32 | Vietnam | APT32 |
| APT33, 34, 35, 39 | Iran | APT33, APT39 |
| APT37, 38 | North Korea | APT37 |
The number is often linked to an internal geographic or actor code used during initial attribution.
“FIN” groups represent financially-motivated threat actors who conduct cybercrime operations such as ATM heists, point-of-sale breaches, or ransomware campaigns.
| Name | Description |
|---|---|
| FIN4 – FIN10 | Groups targeting industries like finance, hospitality, and retail |
| Example: FIN7 | Known for point-of-sale malware and sophisticated phishing campaigns targeting U.S. firms |