

Hello and welcome,
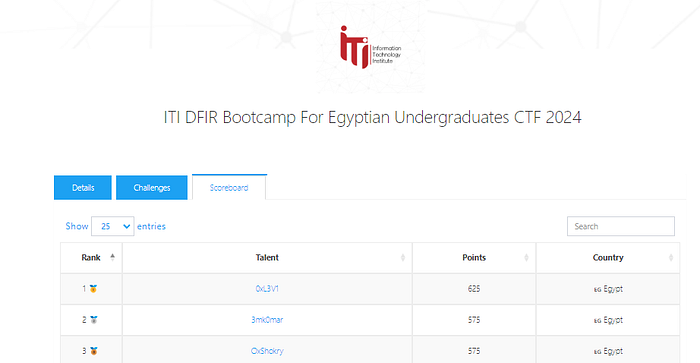
I’m Omar Amir, and I’m thrilled to have achieved 2nd place at the ITI DFIR Bootcamp for Egyptian Undergraduates CTF 2024.
This is my writeup to the hard Memory forensics CTF “Memory Phantom”
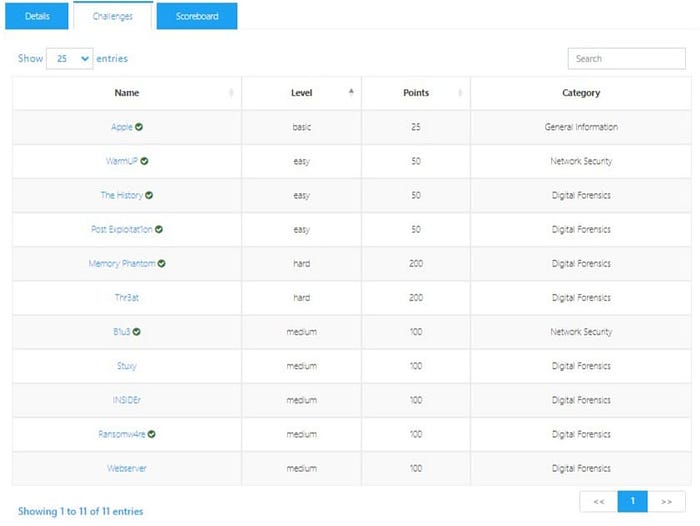
Category: Memory ForensicsLevel: HardPoints: 200
I know that I won’t get the flag by just looking at the processes and finding the malicious ones, as usual in a memory forensics CTF. So, let’s be 200 IQ!
I used
strings MemoryPhantom.raw | grep -i "flag"
#the -i in grep is for case-insensitive search.
Zoom image will be displayed
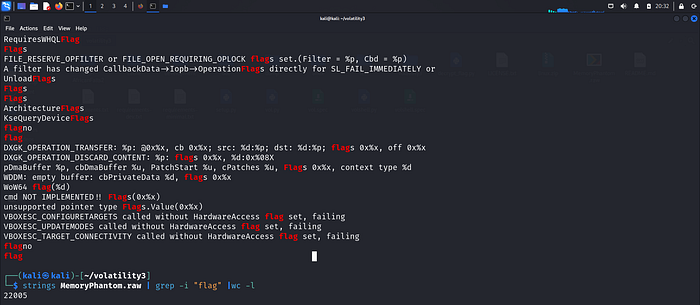
Okay, I got 22,005 results🤡, so let’s be more specific and change it to flag{
Zoom image will be displayed
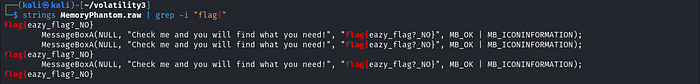
I got clowned again with flag{eazy_flag?_NO}, but I got a message box telling me to check it.
So, I added -C 5 to grep to see what the message contains.
grep -C shows n lines of context around a match.