SIEM (Security Information and Event Management) is a cybersecurity solution that collects, aggregates, normalizes, and analyzes logs and event data from across an organization’s IT infrastructure to detect threats, support incident response, and facilitate forensic investigations.
Log Sources
Host‑Centric Logs
- Windows Event Logs (e.g., login attempts, file access)
- Sysmon (process execution, registry changes)
- Osquery
- Examples:
- User accessing or modifying a file
- Process execution (Event ID 4688)
- Registry key creation or deletion
- PowerShell command execution
Network‑Centric Logs
- Protocols: SSH, VPN, HTTP/S, FTP, SMB
- Examples:
- SSH and VPN connections
- Web traffic and HTTP requests
- File transfers via FTP or network shares
- Outbound data transfer (potential exfiltration)
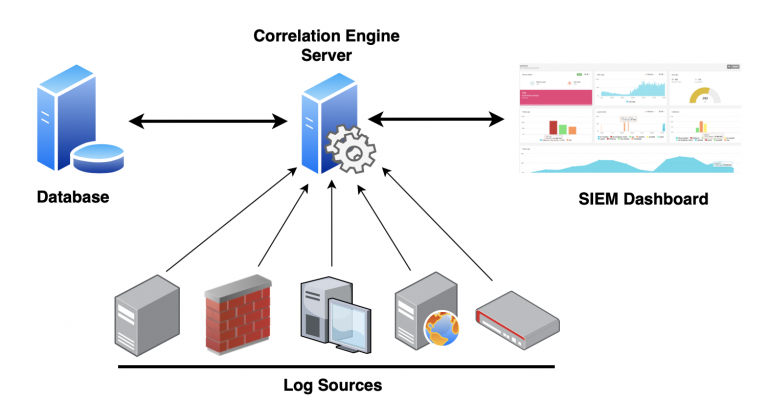
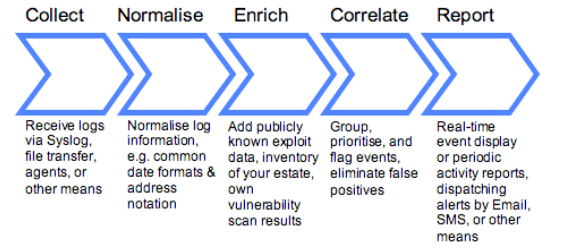
SIEM Architecture and Workflow
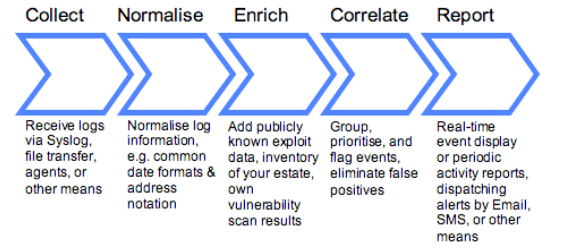
- Data Collection: Agents, port forwarding, or APIs ingest logs in real time.
- Normalization: Convert diverse log formats into a consistent schema.
- Storage: Centralized, scalable repository for short‑ and long‑term retention.
- Correlation & Analytics:
- Rule‑based detection (e.g., threshold, pattern matching)
- Statistical and behavioral analytics
- Alerting & Notification: Generate alerts for suspicious or anomalous events.