During the initial stages of the investigation, it was confirmed that the TryHatMe CEO's host WIN-001 was compromised. The attacker successfully obtained credentials belonging to Cain Omoore, a Domain IT Administrators group member who remotely helped the CEO with the endpoint configuration and cached his credentials on the host.Given the privileges associated with Cain's account, the internal security team suspects that the attacker laterally moved to other systems within the environment or even to Cain's host - WIN-015.Since Cain stores access keys to the TryHatMe factory control system on his WIN-015, your first priority is to investigate his host for any lateral movement or data exfiltration traces. For this, you have been provided with a memory dump of WIN-015. Good luck!
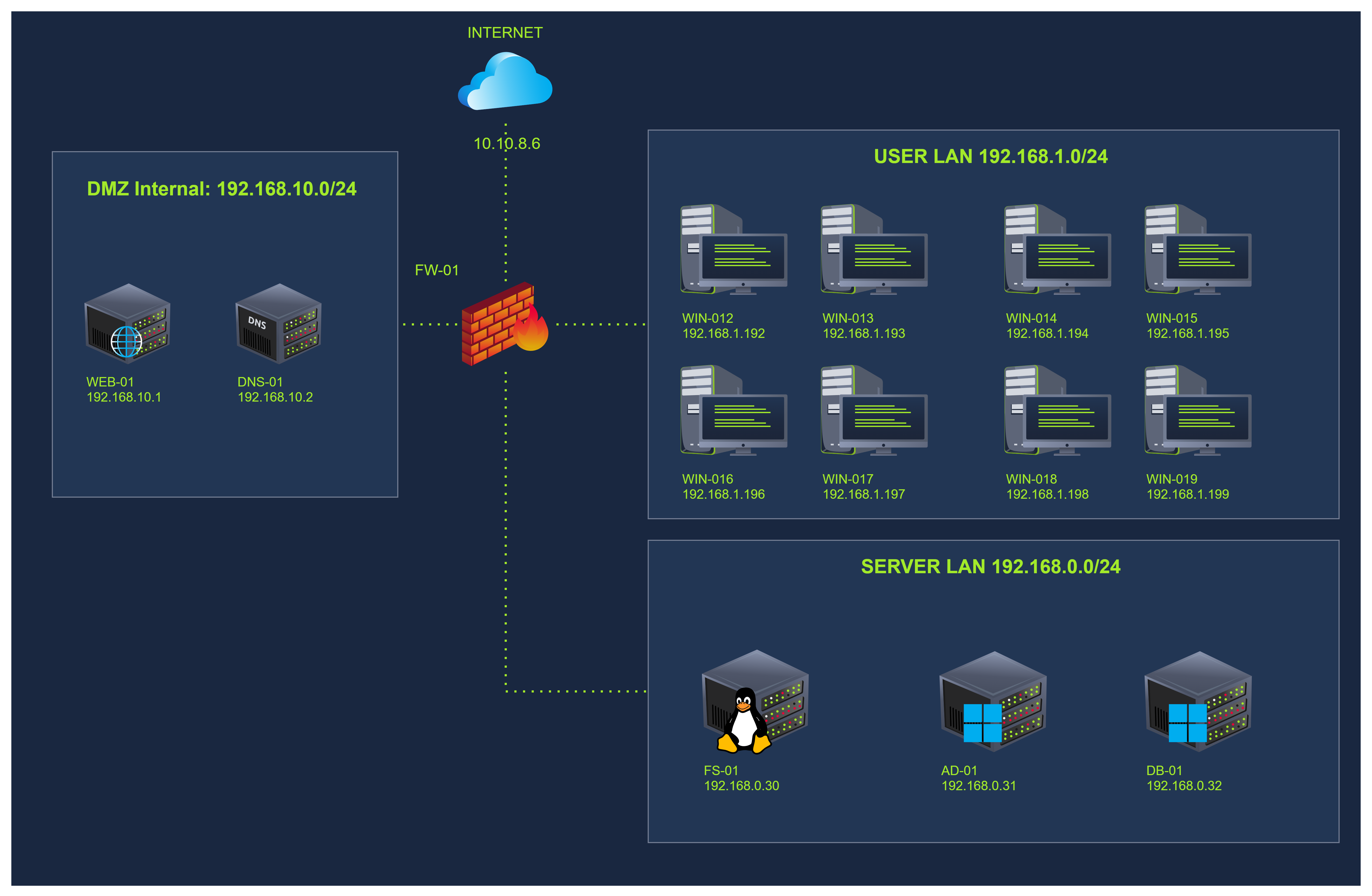
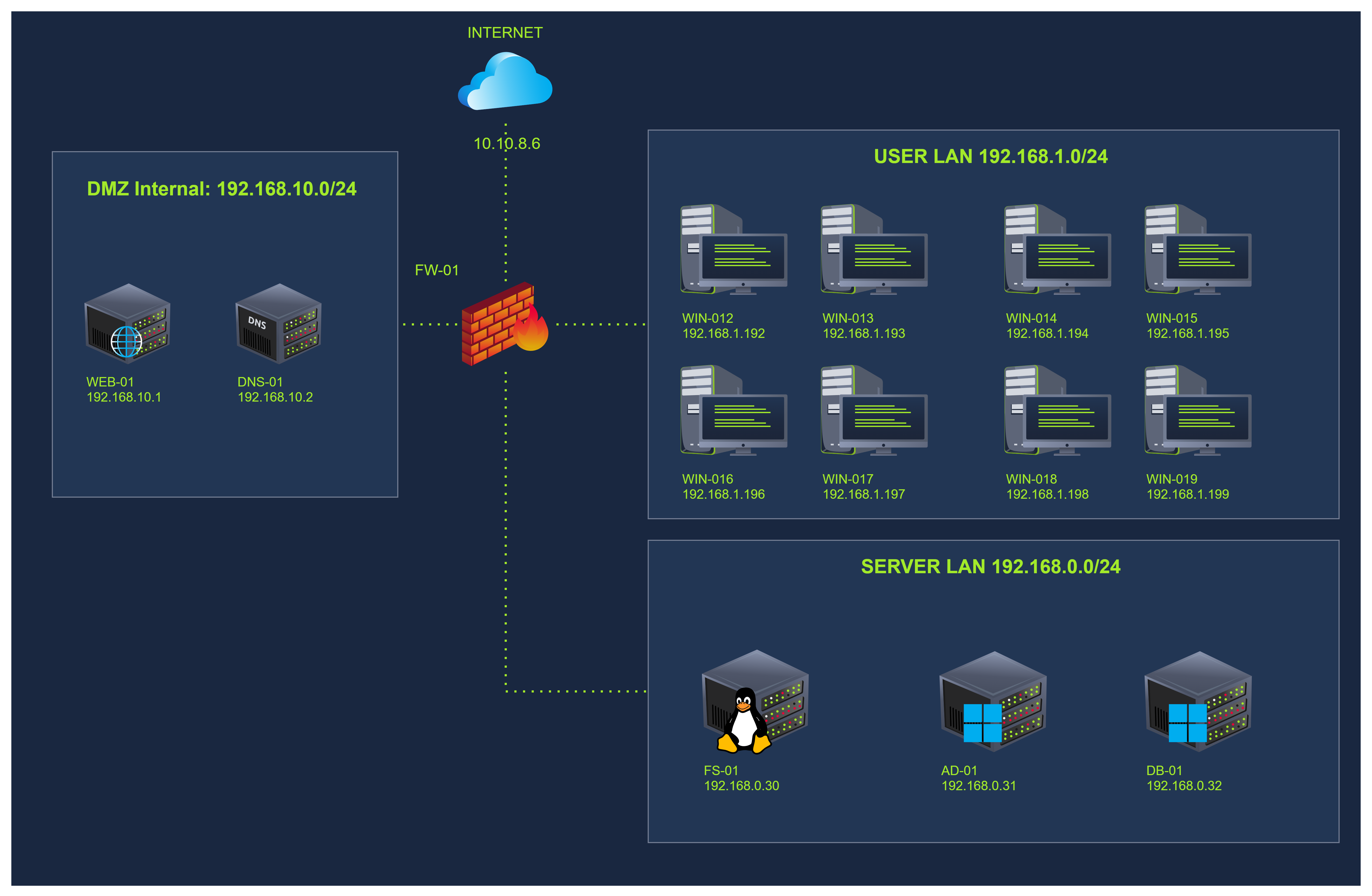
Network Map
https://tryhackme.com/room/supplementalmemory
Below are a few tips on how different lateral movement techniques can be identified using memory analysis.
Detecting Lateral Movement via PsExec Execution
analyst@tryhackme$ vol -f ransomhub.dmp windows.pstree PID PPID ImageFileName
4 0 System
* 272 4 smss.exe
* 384 376 csrss.exe
* 460 376 wininit.exe
* 600 460 services.exe
** 3772 600 psexesvc.exe
*** 3916 3772 512370d.exe
Detecting Lateral Movement via WMI Execution
analyst@tryhackme$ vol -f conti.dmp windows.pstree PID PPID ImageFileName
4 0 System
* 272 4 smss.exe
* 384 376 csrss.exe
* 460 376 wininit.exe
* 600 460 services.exe
** 1244 600 svchost.exe
*** 2416 1244 wmiprvse.exe
**** 5156 2416 cobaltrs.exe
Detecting Lateral Movement via PowerShell Remote
analyst@tryhackme$ vol -f FIN12.dmp windows.pstree PID PPID ImageFileName
4 0 System
* 272 4 smss.exe
* 384 376 csrss.exe
* 460 376 wininit.exe
* 600 460 services.exe
** 1280 600 svchost.exe
*** 2532 1280 wsmprovhost.exe
**** 4896 2532 cmd.exe
***** 5012 4896 conhost.exe
***** 5144 4896 trickbot.exe

WmiPrvSE.exe normally hosts WMI providers (e.g., handling WMI queries internally) and does not usually launch user-facing applications; seeing it spawn TeamsView.exe is anomalous. Also note that TeamsView.exe immediately issues reconnaissance commands (systeminfo, ipconfig, whoami), further flagging its malicious role.