The Update Sequence Number Journal is NTFS’s change‑journal for file‑system‑level events. Every time a file or directory is created, modified, renamed, or deleted, an entry is appended. This lets applications synchronize rapidly by querying only “what changed since X”.
File name: \\$Extend\\$UsnJrnl
Structure of USNJrnl
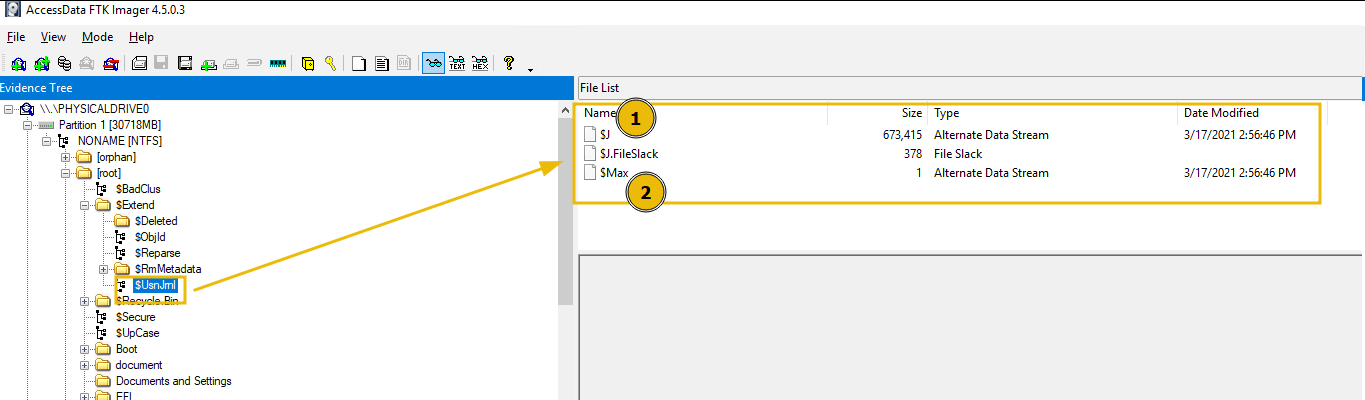
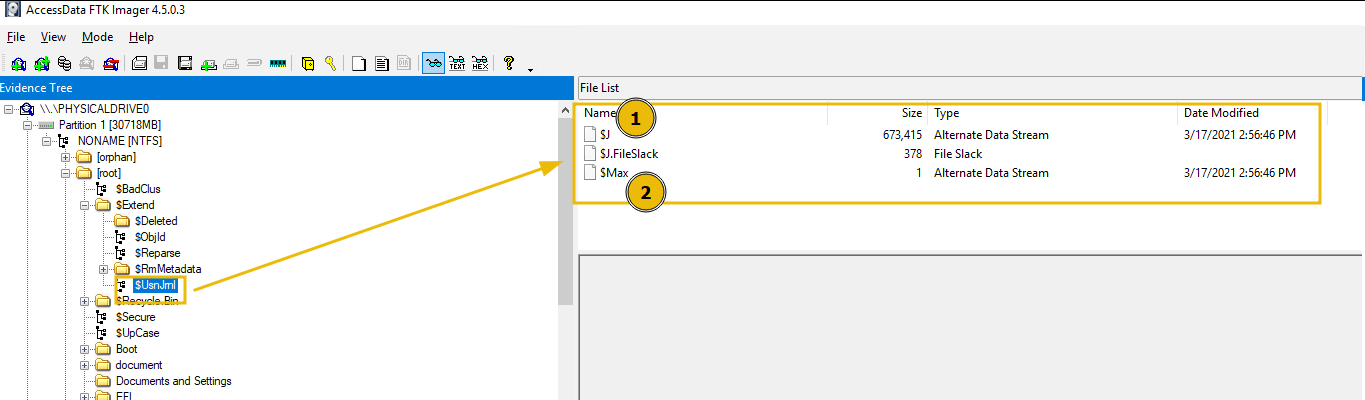
$USNJrnl is the metadata file, which is further comprised of two components, which will be shown if we double-click on the $USNJrnl file, as shown below:
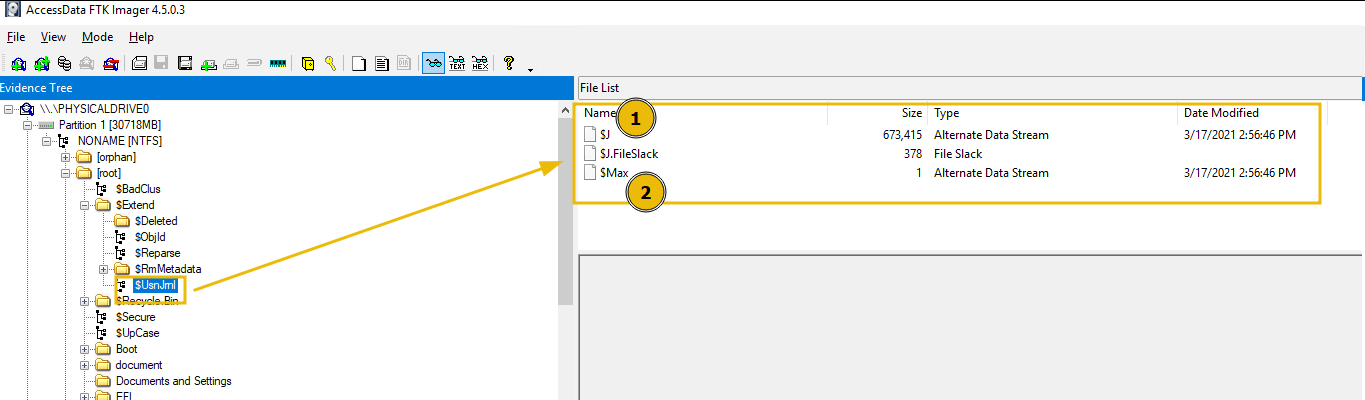
The two components are explained below:
- $Max: Defines the maximum size of the journal and its allocation policy.
- $J: Stores the actual change records. $J is the actual file we are interested in investigating.
- $J, in fact, was implemented as an ADS (Alternative data stream) in NTFS.
Forensics Value
- Comprehensive Change History
- Provides an append‑only, time‑stamped record of file‑system events (create, write, rename, delete, attribute change).
- Even if a file is deleted, its last USN entry typically persists until the journal wraps, giving clues about its existence and characteristics.
- Path & Context Reconstruction
- FRN + parent‑FRN values let you rebuild the full directory path at the moment of each event essential for proving where a suspicious file lived.
- Activity Correlation & Pattern Detection
- Bulk or scripted actions (e.g., ransomware mass‑renames, automated exfiltration) stand out as clusters of similar USN_REASON flags and narrow time windows.
- Efficient Filtering
- Investigators can query “changes since USN X” to zoom in on only the relevant time period—avoiding full‑volume scans and speeding analysis.
- Malware & Insider Threat Tracking
- Stealthy or low‑volume modifications (e.g., dropping a backdoor DLL) still generate USN entries, making it hard for adversaries to operate entirely “under the radar.”